Introduction to NERC CIP Vulnerability Assessment

Compliance to cybersecurity standards, such as NERC CIP, can become an opportunity for organizations to establish standardized processes and gain efficiency. In the electric industry, this opportunity means building a culture of risk assessment and mitigation across all the parties involved with managing, regulating, and overseeing the grid, with the goal of maintaining a more secure and reliable grid in the process. CIP-010 Requirement R3 stipulates that a paper vulnerability assessment (PVA) and an active vulnerability assessment (AVA) need to be performed annually and every three years, respectively.
Vulnerability Assessment Requirements
Per CIP-010, Requirement R3, two types of Vulnerability Assessments are identified. There are requirements for an annual Paper Vulnerability Assessment (PVA) and every-three-years Active Vulnerability Assessment (AVA). For each assessment type, the Guidelines and Technical Basis (G&TB) strongly encourage entities to include at least the following elements, taken from NIST SP 800-115, as well as reviewing this NIST Technical Guide for guidance on approaches and methods to execute each:
- Network Discovery
- Network Port and Service Identification
- Vulnerability Review/Scanning
- Wireless Review/Scanning
Active Vulnerability Assessments vs. Paper Vulnerability Assessments
Per the G&TB in CIP-010, the following are strongly encouraged tasks for a PVA and an AVA, as well as the associated CIP-005, CIP-007, and CIP-010 Requirements and Parts for which they may provide detective controls:
Paper Vulnerability Assessment Tasks
| Task | Description | Requirement Parts |
|---|---|---|
| Network Discovery | A review of network connectivity to identify all Electronic Access Points. | CIP-005 R1 Part 1.2 |
| Network Port and Service Identification | A review to verify that all enabled ports and services have an appropriate business justification. | CIP-007 R1 Part 1.1 |
| Vulnerability Review | A review of security rule-sets and configurations including controls for default accounts, passwords, and network management community strings. | CIP-005 R1 Part 1.3CIP-007 R5 Parts 5.4 – 5.7 |
| Wireless Review | Identification of common types of wireless networks and a review of their controls if they are in any way used for BCS communications. | CIP-005 R1 Part 1.1 |
Active Vulnerability Assessment Tasks
| Task | Description | Requirement Parts |
|---|---|---|
| Network Discovery | Use of active discovery tools to discover active devices and identify communication paths. | CIP-005 R1 Parts 1.1 – 1.2 |
| Network Port and Service Identification | Use of active discovery tools to discover open ports and services. | CIP-007 R1 Part 1.1CIP-010 R1 Parts 1.1.2 – 1.1.4 |
| Vulnerability Scanning | Use of a vulnerability scanning tool to identify known vulnerabilities associated with services running on open ports. | CIP-007 R2 Part 2.3CIP-007 R5 Parts 5.2, 5.4 – 5.7 |
| Wireless Scanning | Use of a wireless scanning tool to discover wireless signals and networks in the physical perimeter of a BCS. | CIP-005 R1 Part 1.1 |
While both PVA and AVA tasks are used as detective controls for complying with the above requirements, the controls provided in AVA tasks are more effective. At a high level, the review of evidence in PVA tasks simply identify issues associated with the documenting and/or maintaining of that evidence. AVA tasks, however, include the collection of fresh (updated) evidence that is reviewed and analyzed. AVA tasks can not only identify those documentation issues, they can also identify issues associated with processes followed to meet their respective compliance obligations. As an example, the review of network port and service evidence in a PVA assumes that port and service list is accurate when identifying missing or insufficient business justifications. In an AVA, the network port and service assessment adds the compilation of a fresh network port and service list to compare to existing evidence. This comparison can shine a light on issues related to the methods followed when the list of ports and services were initially collected, how dynamic port ranges associated with services were determined, or if unaccounted for software was installed enabling a previously undocumented port.
As described above, executing PVAs and AVAs have a much greater importance to an entity’s CIP compliance program than simply complying with CIP-010 Requirement 3 Parts 3.1 and 3.2. While automating PVA and AVA tasks improve the efficiency with which the tasks can be executed, that automation also eliminates instances of potential human error when executing the tasks. Thus, an automated solution, such as NP-View, can play an important role to assist entities with automating a number of the tasks above. NP-View is also leveraged by NERC regional auditors for validating evidence during audits.
Reviewing network path originating from or terminating at the ESP to verify interactive remote access
Preparation
In either a PVA or AVA, one key factor for success is a detailed VA plan, which should include:
- Roles and responsibilities
- Preparation, including:
- Personal protective equipment requirements,
- Site access requests,
- System access requests,
- Change request tickets, and
- VA data storage location.
- Data collection
- Onsite activities
- Data analysis
Another key success factor is entity subject matter expert (SME) engagement in the VA process. Regardless of how well versed the VA team members are in the VA process, inaccurate or incomplete data collected from the Cyber Assets ensures an unsuccessful VA. Additionally, SMEs typically provide the VA team with a more detailed view of the networks than can be collected from network diagrams alone.
Requirements
At a minimum, the needed data inputs for conducting a NERC CIP Vulnerability Assessment include:
- NERC CIP Cyber Asset Inventory lists, including:
- Unique identifier, such as hostname,
- IP addresses and subnet mask, and
- Electronic Security Perimeter (ESP).
- List of Intermediate Systems,
- List of ESP networks with included network subnets and their respective Electronic Access Points (EAPs),
- CIP-007 R1 Part 1.1 ports and services justification evidence, and
- CIP-007 R5 Parts 5.4 – 5.7 password controls evidence.
- Configuration files in format readable by NP View
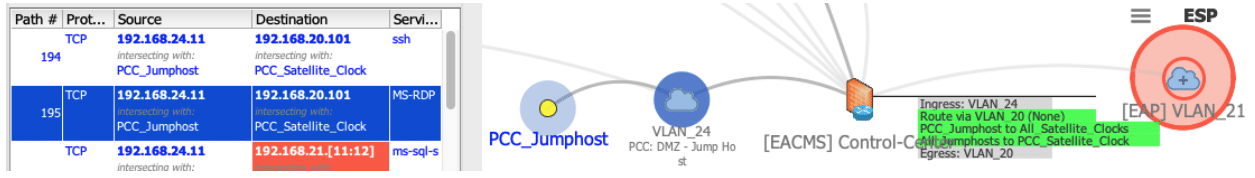
NP-View uses device configuration files from firewalls, routers, and switches to create a network diagram that allows compliance auditors and other users to understand objects, routes, permissions, and policies in a user readable format. To input the device files in the correct format, follow the instructions on the NP Knowledge Base. If a particular hardware/software platform is not supported, please contact support@network-perception.com to start the implementation of a new configuration parser.
Next Steps
Having a thorough, efficient, and repeatable methodology for vulnerability assessments lays the groundwork for its successful execution. Executing that methodology with personnel that both have expertise in the NERC CIP Reliability Standards and experience conducting vulnerability assessments with automated tools is crucial to that success. NP-View allows those executing vulnerability assessments to more efficiently complete a number of the tasks while minimizing the risk of human error during the more tedious ones. The time saving and completeness aspects are critical as network environment becomes more complex and our resources remain limited.
This introduction is part of the Better, Faster NERC CIP Vulnerability Assessments Using NP-View white paper, which includes additional information and step-by-step instructions on how to best leverage NP-View during your CVA. For any questions or feedback, please feel free to contact the Network Perception team or the Network & Security Technologies (N&ST) team who co-wrote the white paper.